Why this eBook?
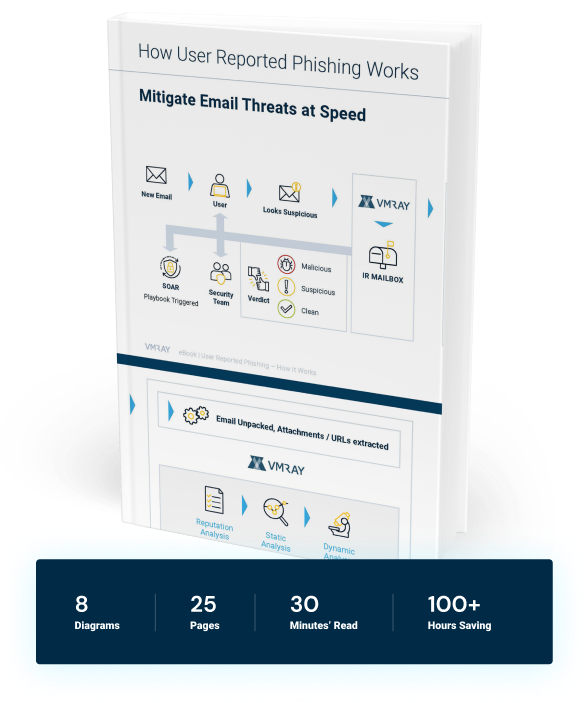
Download this User Reported Phishing eBook and learn how VMRay can help speed incident response with automated phishing triage and analysis:
- Understand the value of automating Tier 1 Analyst analysis with SOAR playbook integration into the VMRay threat detection and analysis platform
- Learn the benefits of security automation and how it can help your SOC team reduce time-consuming false positives
- Realize the value and cost savings security automation provides when dealing with advanced malware and phishing threats to dramatically reduce mean time to detect (MTTD) and respond (MTTR) to malicious email threats.