70 organizations in public sector, military, and critical infrastructure trust VMRay to transform the maturity of their SOC and performance of Threat Intelligence curation

PRIVACY
CUSTOMER STORY
“VMRay’s analysis, known for its reliability and precision, has become the cornerstone of our robust security posture, enabling us to build actionable threat intelligence against the specific threats we face.”
CUSTOMER STORY
“Our search for a better sandbox has finally ended with VMRay. The depth of analysis, and the reliability of reports surpasses anything we’ve encountered in the past.”
GOVERNMENT CYBERSECURITY


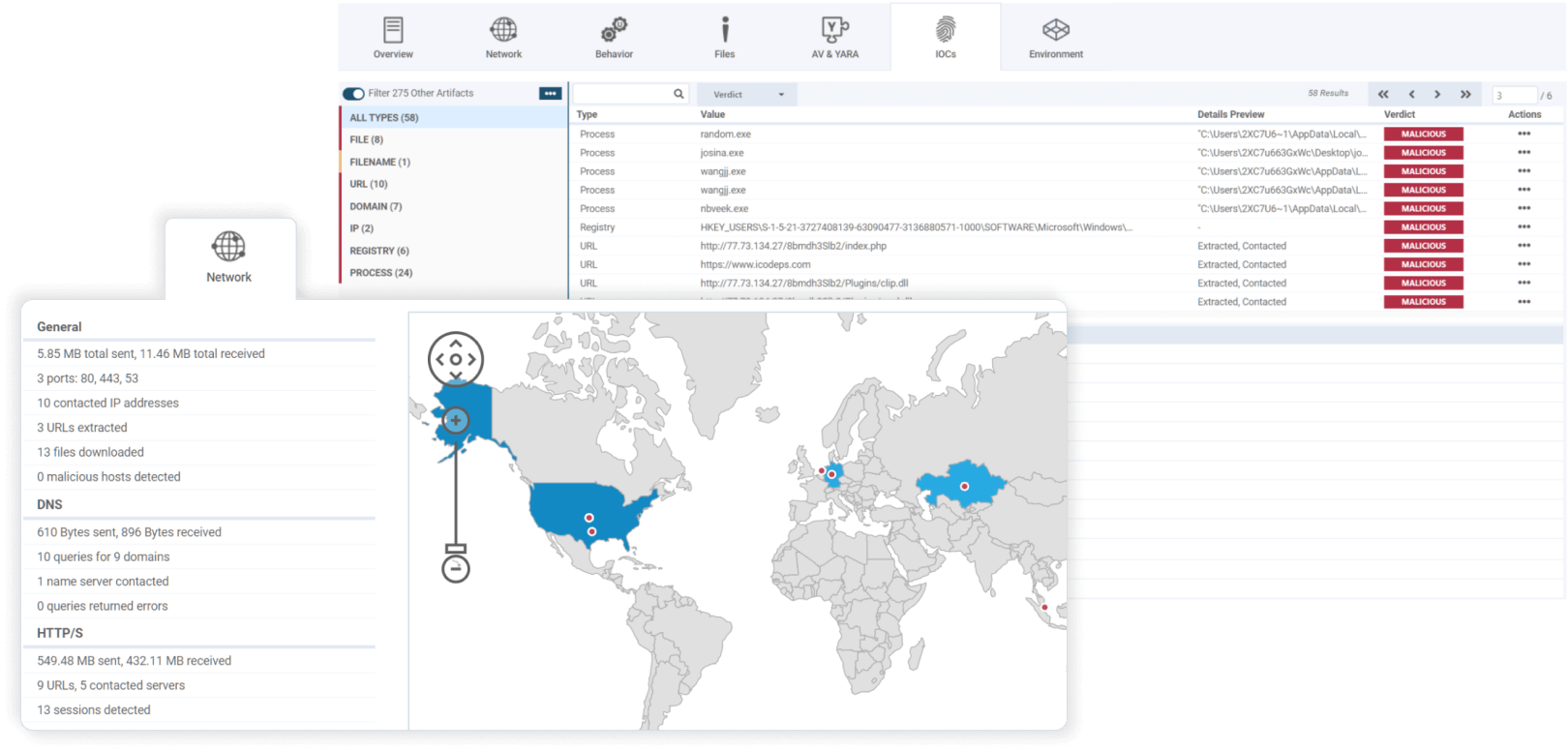
advanced malware & phishing threats
Fast and in-depth analysis. Reliable and relevant output.
“VMRay’s unparalleled analysis quality not only empowered us to conquer previously unknown threats with evasion resistance but inspired the expansion of our utilization into automated security workflows.”
Head of Incident Response
Intra-governmental organization in Europe
RESOURCES
From VMRay Academy >

Read the white paper >
Read the ebook >
Automate time-consuming security tasks and create room for maturing your SOC.
Get simple and definitive verdict on what is malicious, suspicious or benign for all of your EDR and SOAR alerts
SEAMLESS INTEGRATIONS

VMRay Professional Services and Support for Onboarding, Deployment and Integrations
“The technical prowess of VMRay's customer support has been nothing short of impressive. Their expertise and to-the-point assistance have become invaluable for our team.”
Head of Incident Response
Intra-governmental organization in Europe
ANNUAL SUPPORT

GOVERNMENT CYBERSECURITY


Check our latest insights on malware, phishing, sandboxing, AI in cybersecurity, and much more.
Browse the courses about alert handling, deep threat analysis and response, threat intelligence generation and more.
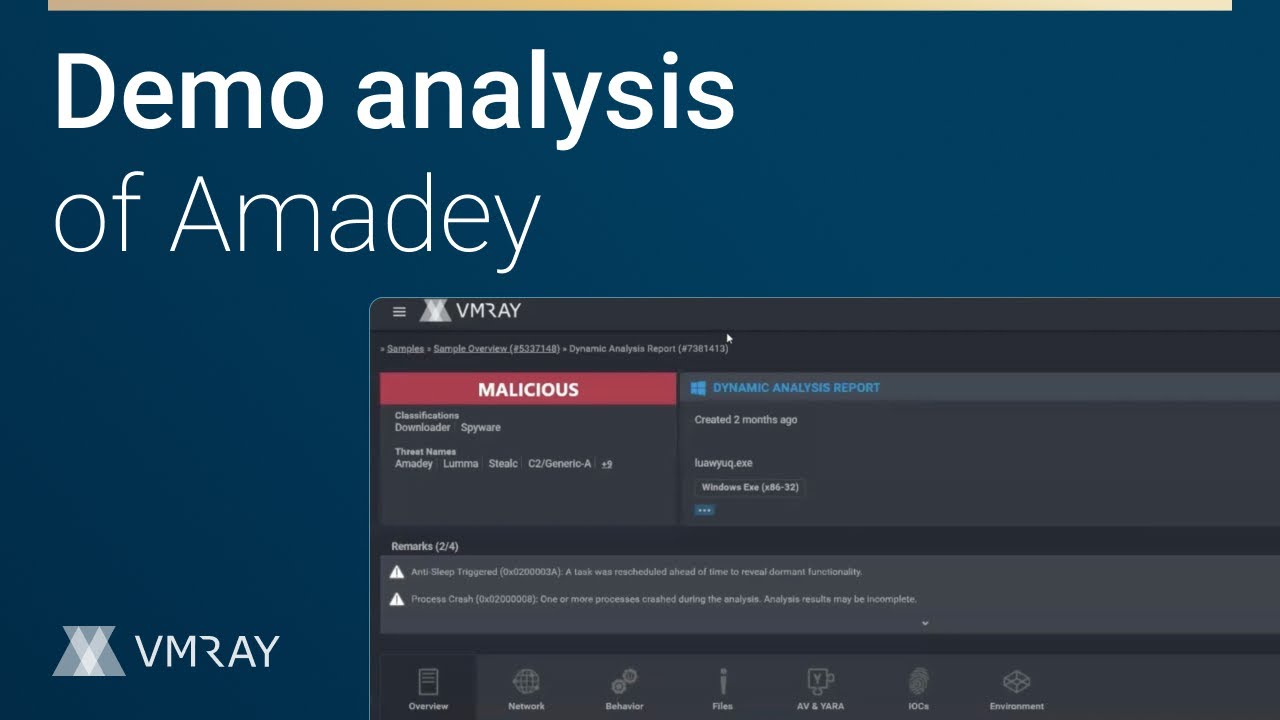
See real-world examples of VMRay’s best-in-class malware analysis and detection platform.




