radiance.png.exe
Created at 2019-05-16T17:08:00
Remarks (2/3)
(0x200000e): The overall sleep time of all monitored processes was truncated from "21 hours, 36 minutes, 10 seconds" to "1 minute, 34 seconds" to reveal dormant functionality.
(0x200003a): A task was rescheduled ahead of time to reveal dormant functionality.
VMRay Threat Indicators (33 rules, 126 matches)
| Severity | Category | Operation | Count | Classification | |
|---|---|---|---|---|---|
|
5/5
|
Local AV | Malicious content was detected by heuristic scan | 1 | - | |
|
|||||
|
5/5
|
Reputation | Known malicious file | 1 | Trojan | |
|
|||||
|
4/5
|
Information Stealing | Exhibits Spyware behavior | 1 | Spyware | |
|
|||||
|
4/5
|
Injection | Writes into the memory of another running process | 2 | - | |
|
|||||
|
|||||
|
4/5
|
Injection | Modifies control flow of another process | 1 | - | |
|
|||||
|
4/5
|
Reputation | Known malicious URL | 2 | - | |
|
|||||
|
|||||
|
3/5
|
OS | Disables a crucial system service | 2 | - | |
|
|||||
|
|||||
|
3/5
|
Network | Reads network adapter information | 1 | - | |
|
|||||
|
3/5
|
Anti Analysis | Delays execution | 2 | - | |
|
|||||
|
|||||
|
3/5
|
Network | Connects to TOR hidden service | 1 | - | |
|
|||||
|
3/5
|
Persistence | Schedules task for system startup | 1 | - | |
|
|||||
|
2/5
|
Anti Analysis | Resolves APIs dynamically to possibly evade static detection | 1 | - | |
|
|||||
|
2/5
|
Information Stealing | Reads sensitive browser data | 4 | - | |
|
|||||
|
|||||
|
|||||
|
|||||
|
2/5
|
Information Stealing | Reads sensitive mail data | 1 | - | |
|
|||||
|
2/5
|
Information Stealing | Reads sensitive ftp data | 1 | - | |
|
|||||
|
2/5
|
Information Stealing | Reads sensitive application data | 2 | - | |
|
|||||
|
|||||
|
2/5
|
Anti Analysis | Tries to detect virtual machine | 1 | - | |
|
|||||
|
2/5
|
Network | Sets up server that accepts incoming connections | 1 | Backdoor | |
|
|||||
|
1/5
|
Process | Creates process with hidden window | 3 | - | |
|
|||||
|
|||||
|
|||||
|
1/5
|
Device | Monitors keyboard input | 1 | Keylogger | |
|
|||||
|
1/5
|
Process | Creates system object | 1 | - | |
|
|||||
|
1/5
|
Process | Creates a page with write and execute permissions | 2 | - | |
|
|||||
|
|||||
|
1/5
|
Process | Reads from memory of another process | 2 | - | |
|
|||||
|
|||||
|
1/5
|
Information Stealing | Possibly does reconnaissance | 3 | - | |
|
|||||
|
|||||
|
|||||
|
1/5
|
Network | Performs DNS request | 3 | - | |
|
|||||
|
|||||
|
|||||
|
1/5
|
Process | Overwrites code | 1 | - | |
|
|||||
|
1/5
|
Network | Connects to remote host | 1 | - | |
|
|||||
|
1/5
|
Network | Connects to HTTP server | 5 | - | |
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
1/5
|
Network | Connects to HTTPS server | 71 | - | |
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
1/5
|
Network | Tries to connect using an uncommon port | 4 | - | |
|
|||||
|
|||||
|
|||||
|
|||||
|
1/5
|
Process | Process crashed | 1 | - | |
|
|||||
|
1/5
|
Static | Unparsable sections in file | 1 | - | |
|
|||||
|
0/5
|
Process | Enumerates running processes | 1 | - | |
|
|||||
Screenshots
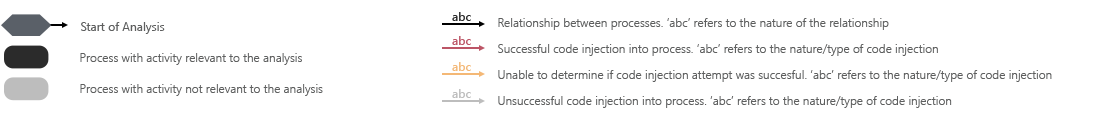
Monitored Processes
Sample Information
Analysis Information
| Creation Time | 2019-05-16 19:08 (UTC+2) |
| Analysis Duration | 00:04:18 |
| Number of Monitored Processes | 48 |
| Execution Successful |

|
| Reputation Enabled |

|
| WHOIS Enabled |

|
| Local AV Enabled |

|
| YARA Enabled |

|
| Number of AV Matches | 1 |
| Number of YARA Matches | 0 |
| Termination Reason | Timeout |
| Tags |