EB54.tmp.exe
Created at 2019-05-13T17:21:00
Remarks (2/2)
(0x200003a): 2 tasks were rescheduled ahead of time to reveal dormant functionality.
VMRay Threat Indicators (17 rules, 55 matches)
| Severity | Category | Operation | Count | Classification | |
|---|---|---|---|---|---|
|
5/5
|
Local AV | Malicious content was detected by heuristic scan | 7 | - | |
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
5/5
|
Reputation | Known malicious file | 1 | Trojan | |
|
|||||
|
4/5
|
Network | Modifies network configuration | 1 | - | |
|
|||||
|
4/5
|
Reputation | Known malicious URL | 17 | - | |
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
3/5
|
Anti Analysis | Delays execution | 1 | - | |
|
|||||
|
2/5
|
Anti Analysis | Resolves APIs dynamically to possibly evade static detection | 1 | - | |
|
|||||
|
2/5
|
Reputation | Known suspicious file | 5 | Trojan | |
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
1/5
|
Persistence | Installs system startup script or application | 1 | - | |
|
|||||
|
1/5
|
Process | Creates process with hidden window | 2 | - | |
|
|||||
|
|||||
|
1/5
|
File System | Modifies operating system directory | 1 | - | |
|
|||||
|
1/5
|
Information Stealing | Reads system data | 1 | - | |
|
|||||
|
1/5
|
Process | Creates system object | 1 | - | |
|
|||||
|
1/5
|
Process | Overwrites code | 1 | - | |
|
|||||
|
1/5
|
Network | Downloads executable | 4 | Downloader | |
|
|||||
|
|||||
|
|||||
|
|||||
|
1/5
|
Network | Connects to HTTP server | 9 | - | |
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
|||||
|
1/5
|
PE | Drops PE file | 1 | Dropper | |
|
|||||
|
0/5
|
Process | Enumerates running processes | 1 | - | |
|
|||||
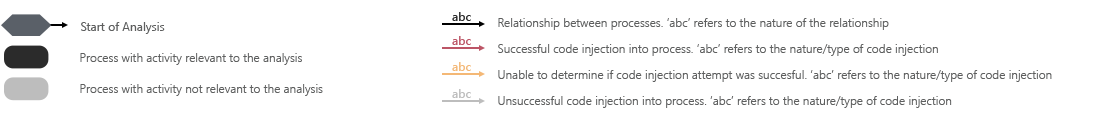
Screenshots
Monitored Processes
Sample Information
Analysis Information
| Creation Time | 2019-05-13 19:21 (UTC+2) |
| Analysis Duration | 00:04:49 |
| Number of Monitored Processes | 12 |
| Execution Successful |

|
| Reputation Enabled |

|
| WHOIS Enabled |

|
| Local AV Enabled |

|
| YARA Enabled |

|
| Number of AV Matches | 7 |
| Number of YARA Matches | 0 |
| Termination Reason | Timeout |
| Tags |