539b0b5d54757e8a2b754ecdc2939eb7cf9db0ed1728e0eca407500222668505 (SHA256)
fcr.exe
Created at 2018-09-23 19:12:00
Notifications (2/3)
Some extracted files may be missing in the report since the maximum number of extracted files was reached during the analysis. You can increase the limit in the configuration settings.
The overall sleep time of all monitored processes was truncated from "1 minute" to "20 seconds" to reveal dormant functionality.
The operating system was rebooted during the analysis.
Top Threat Indicators (View all 550 threat indicators)
| Category | Operation | Classification |
|---|---|---|
| File System | Encrypts content of user files | Ransomware |
| OS | Modifies system security configuration | - |
| Persistence | Installs system startup script or application | - |
Screenshots
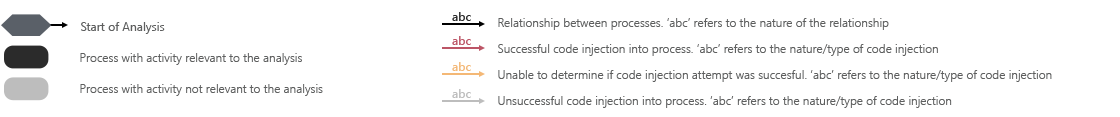
Monitored Processes
Analysis Information
| Creation Time | 2018-09-23 21:12 (UTC+2) |
| Analysis Duration | 00:05:24 |
| Number of Monitored Processes | 3 |
| Execution Successful |

|
| Reputation Enabled |

|
| WHOIS Enabled |

|
| YARA Enabled |

|
| Termination Reason | Timeout |
| Tags |
Sample Information
Analyzer Information
| Dynamic Analyzer Build Date | 2018-07-24 20:08 (UTC+2) |
| Dynamic Analyzer Version | 2.4.0 |
| Static Analyzer Version | 1.0.0 |
| VTI Ruleset Version | 3.0 |
| YARA Built-in Ruleset Version | 1.0 |
| Analysis Report Layout Version | 3 |